Microsoft Integration: GDAP
BEFORE YOU BEGIN To review prerequisites and learn how to fully set up an integration with Microsoft in IT Glue, refer to Microsoft Integration.
Microsoft’s GDAP follows the principle of least privilege for access control. As follows are the three important steps to perform in Microsoft Azure to set up granular delegated admin permissions (GDAP):
- Creating a service account user for GDAP.
- Creating a new security group and assigning the service account user to the group.
NOTE It is required to assign this security group to each GDAP relationship for all the tenants.
- Configuring the IT Glue application with proper permissions.
NOTE Both Delegated and Application permissions are required to be added.
Creating a service account user for GDAP
IMPORTANT The procedure in this section is required for only granular delegated admin permissions (GDAP) tenants and not relevant for delegated admin permissions (DAP).
- Log in to your Microsoft Azure portal.
- From the left navigation menu, navigate to Microsoft Entra ID > Users.
- From the New user drop-down menu, select Create new user.
- Fill in the required fields.
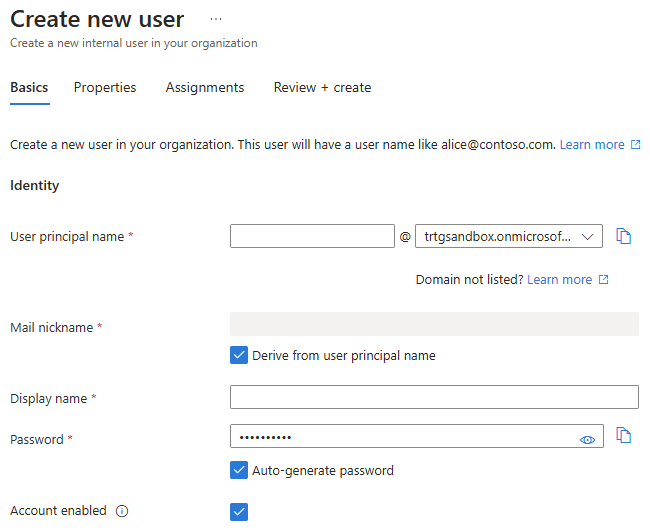
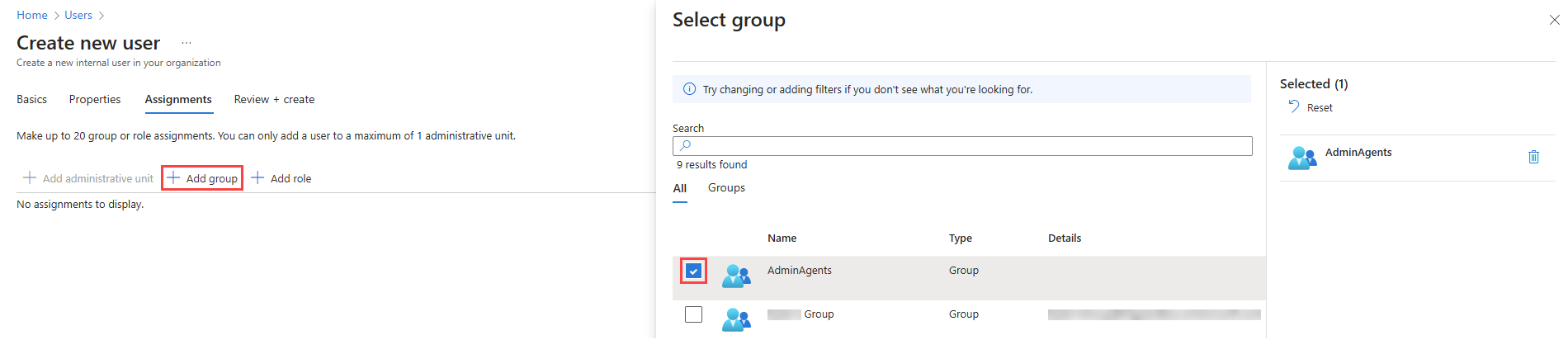
- Click the Assignments tab.
- Click Add group.
- Select the AdminAgents group check box, and click Select at the bottom of the page.
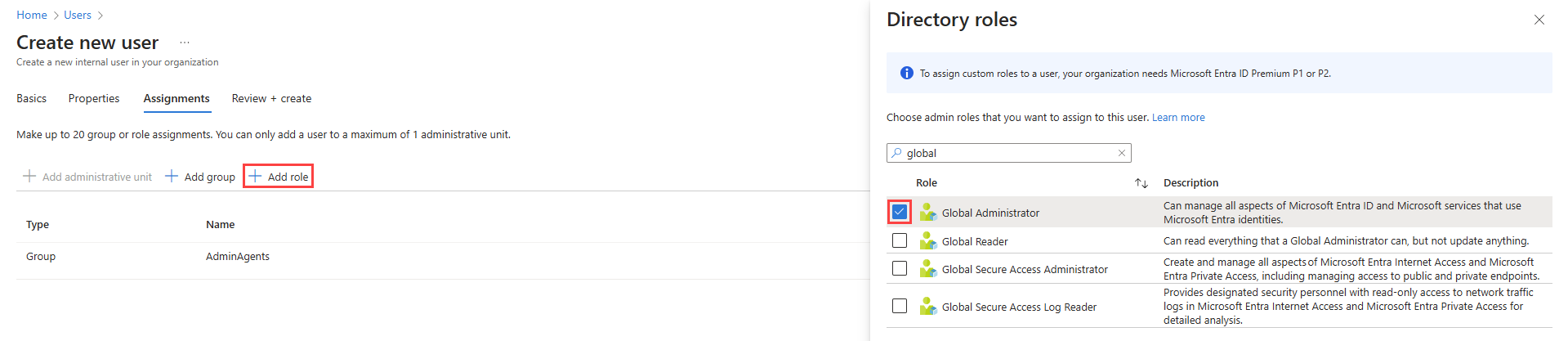
- Click Add role.
- Select the Global Administrator role check box, and click Select at the bottom of the page.
- Create the new service account user.
NOTE MFA must be enabled for this service account.
Creating a new security group
Create a new security group in Microsoft Azure and add the service account user to the group as follows:
- From the left navigate menu, navigate to Microsoft Entra ID > Groups.
- Click New group.
- Fill in the required fields, leaving the Group type as the default option, Security.
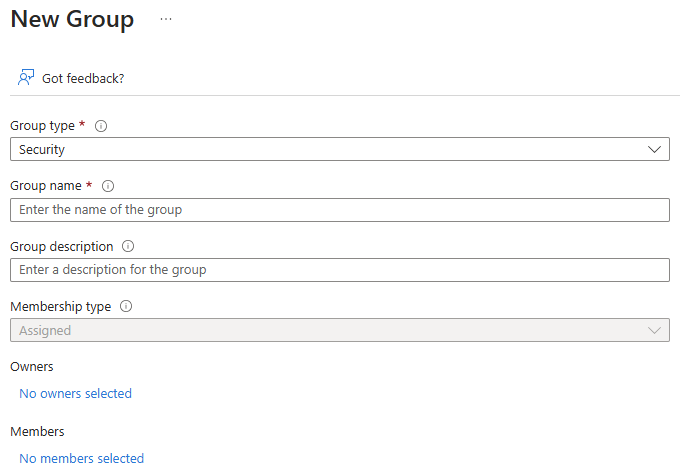
- In the Members section, click No members selected.
- Select the service account user created in Creating a service account user for GDAP, and click Select at the bottom of the page to add the user to the group.
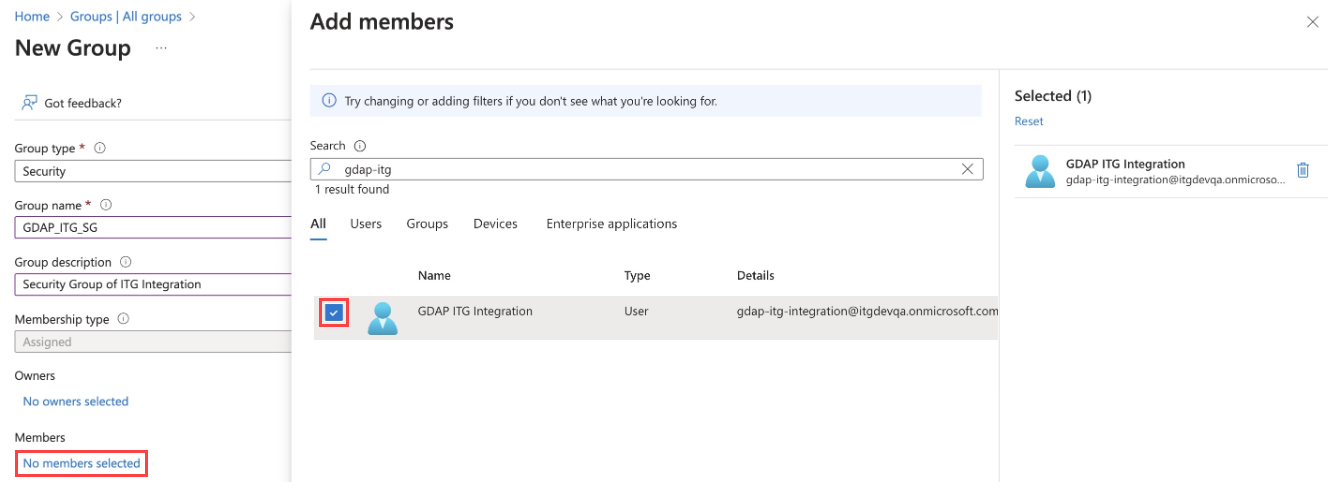
- Click Create to create the security group.
- From Microsoft Partner Center, assign this security group to the GDAP relationship that includes the service account created in the previous section. You must ensure that this security group is assigned to each GDAP relationship and has at least one of the following permissions:
- Global Administrator
- Privileged Role Administrator
- Cloud Application Administrator
- Global Reader
- Intune Administrator
- Insights Business Leader
- Reports Reader
If you assign any permission other than Global Administrator (Privileged Role Administrator or Cloud Application Administrator), the following permissions are required to be assigned:
For more information, refer to Obtain granular admin permissions to manage a customer's service and Grant granular permissions to security groups in the Microsoft Partner Center documentation.
Configuring the IT Glue application with proper permissions
For instructions, refer to Register IT Glue as an application in your Microsoft account in Microsoft Integration.
NOTE The Redirect URI field is required for users setting up GDAP.
NA: https://[subdomain].itglue.com/microsofts
EU: https://[subdomain].eu.itglue.com/microsofts
AU: https://[subdomain].au.itglue.com/microsofts
Retrieving the client ID, tenant ID, and client secret value to activate the integration in IT Glue
For instructions, refer to Copy your client ID and tenant ID from Microsoft and Generate and copy your client secret value in Microsoft in Microsoft Integration.
Configuring API access permissions
For instructions, refer to Configure API access permissions in Microsoft in Microsoft Integration.



